A new type of malware takes a decidedly more stealthy and hard-to-remove path into your OS — it hides in your BIOS chip and thus remains even after you reinstall your OS or format your hard drive.
Kaspersky has observed the growth of Unified Extensible Firmware Interface (UEFI) firmware malware threats since 2019, with most storing malware on the EFI System Partition of the PC’s storage device. However, a sinister development had earlier been spotted with a new UEFI malware, detected by Kasperksy’s firmware scanner logs, that implants malicious code into the motherboard’s Serial Peripheral Interface (SPI) Flash. The security researchers have dubbed this flash-resident UEFI malware ‘MoonBounce’.
Dangerous MoonBounce Malware
MoonBounce isn’t the first UEFI malware discovered in the wild that targets SPI flash. Kaspersky says that the likes of LoJax and MosaicRegressor came before it. However, MoonBounce shows “significant advancement, with a more complicated attack flow and greater technical sophistication.” It also seems to have infected a machine remotely.
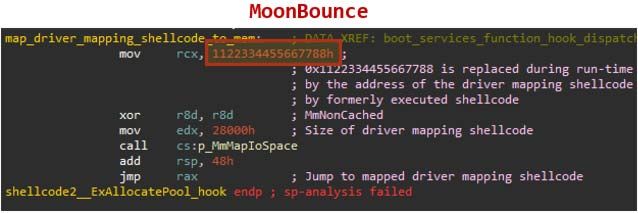
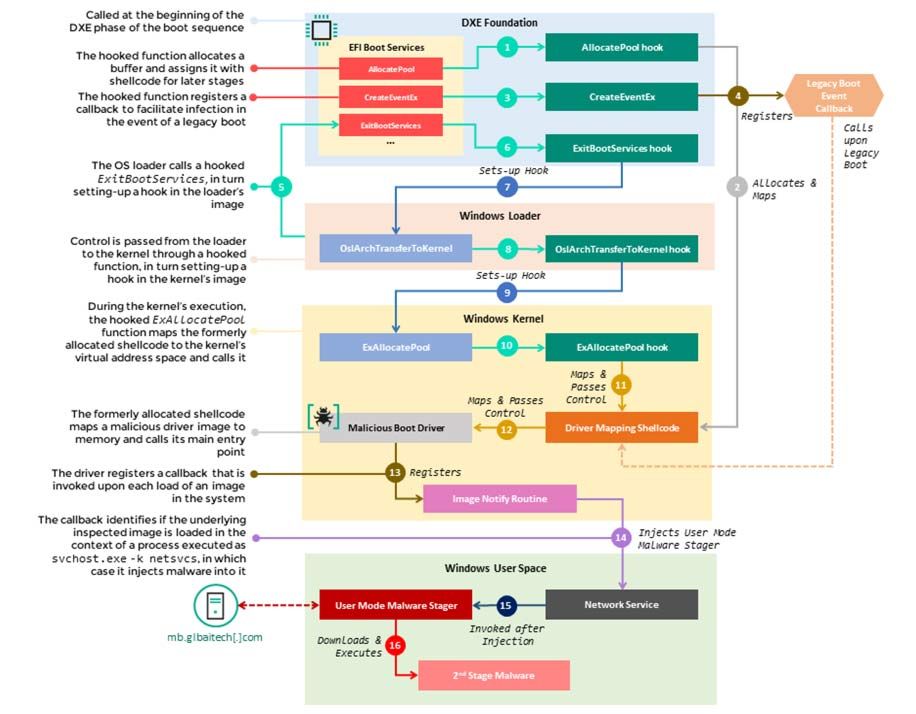
MoonBounce is undeniably clever in the way it gets into a system and makes itself hard to detect and dispose of. “The source of the infection starts with a set of hooks that intercept the execution of several functions in the EFI Boot Services Table,” explains Kaspersky on its SecureList blog. The hooks are then used to divert function calls to the malicious shellcode that the attackers have appended to the CORE_DXE image. This, in turn, “sets up additional hooks in subsequent components of the boot chain, namely the Windows loader,” said the security researchers. This allows the malware to be injected into an svchost.exe process when the computer boots into Windows.
Transport Technology Company the Only Logged Attack so Far
Of course, Kaspersky was interested to see what the malware would do next. So, on an infected machine, the researchers observed the malware process try and access a URL to fetch the next stage payload and run it in memory. Interestingly, this part of the sophisticated attack didn’t seem to go anywhere, so it wasn’t possible to analyze any further steps in MoonBounce. Perhaps this malware was still in testing when it was spotted, and/or it is being held back for special purposes. In addition, the malware isn’t file-based and does at least some of its operations only in memory, making it hard to see exactly what MoonBounce did on the single host PC on a company’s network.
A single machine, owned by a transportation company, seems to be the only machine on Kaspersky’s logs that has a MoonBounce infection in its SPI Flash. It isn’t certain how the infection took place, but it is thought it was instigated remotely. That sole machine at a transport technology company seems to have spread non-UEFI malware implants to other machines on the network. With much of its work being file-less and memory resident only, it isn’t easy to observe from this single sample.
Below, a flow chart breaks down how MoonBounce boots and deploys from the moment your UEFI PC is switched on, through Windows loading, and into being a usable but infected PC.
APT41 Fingerprints Detected
Another important branch of the work done by security researchers like Kaspersky is looking into who is behind the malware that it discovers, what the purposes of the malware are, and what specific targets the malware is primed for.
Concerning MoonBounce, Kaspersky seems pretty certain that this malware is the product of APT41, “a threat actor that’s been widely reported to be Chinese-speaking.” In this case, the smoking gun is a “unique certificate” that the FBI has previously reported as signaling the use of APT41-owned infrastructure. APT41 has a history of supply chain attacks, so this is a continuation of a central thread of APT41’s nefarious operations.
Safety Measures
To help avoid falling victim to MoonBounce or similar UEFI malware, Kaspersky suggests a number of measures. It recommends users keep their UEFI firmware updated directly from the manufacturer, verify that BootGuard is enabled where available, and enable Trust Platform Modules. Last but not least, it recommends a security solution that scans system firmware for issues so measures can be taken when UEFI malware is detected.
Go to Cybersecurity Knowledge Base
Stay informed of the latest Cybersecurity trends, threats and developments. Sign up for RiSec Weekly Cybersecurity Newsletter Today
Remember, CyberSecurity Starts With You!
- Globally, 30,000 websites are hacked daily.
- 64% of companies worldwide have experienced at least one form of a cyber attack.
- There were 20M breached records in March 2021.
- In 2020, ransomware cases grew by 150%.
- Email is responsible for around 94% of all malware.
- Every 39 seconds, there is a new attack somewhere on the web.
- An average of around 24,000 malicious mobile apps are blocked daily on the internet.



