pipenv is a Python Development Workflow for Humans.
Affected package, versions [2018.10.9, 2022.1.8)
How to fix?
Upgrade pipenv to version 2022.1.8 or higher.
Overview
Affected versions of this package are vulnerable to Arbitrary Command Injection. Due to a flaw in pipenv’s parsing of requirements files, an attacker can insert a specially crafted string inside a comment anywhere within a requirements.txt file, which will cause victims who use pipenv to install the requirements file (e.g. with pipenv install -r requirements.txt) to download dependencies from a package index server controlled by the attacker. By embedding malicious code in packages served from their malicious index server, the attacker can trigger arbitrary remote code execution (RCE) on the victims’ systems.
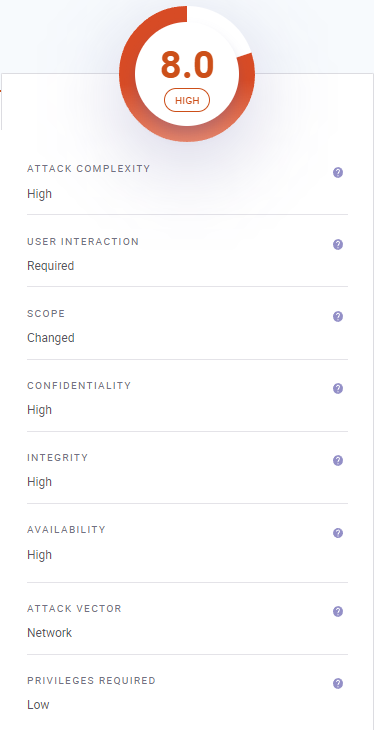
According to the requirements file format specification, any lines which begin with a # character, and/or any text in a line following whitespace and a # character should be interpreted as a comment which will be ignored during the processing of the requirements file.
However, due to a flaw in pipenv’s parsing of requirements files, an attacker can insert a specially crafted string inside a comment anywhere within a requirements.txt file, which will cause victims who use pipenv to install the requirements file
Note: The primary hurdle to successful exploitation of this vulnerability depends on an attacker’s ability to surreptitiously insert a specially crafted string into a requirements.txt file that will be installed by a victim. This is not a highly likely scenario, however, it can be made easier to obfuscate due to it being hidden within comments.
References
- WH Smith Announces Cyber-Attack: Employee Data Stolen - 2 March 2023
- What distinguishes Application Security from API Security? - 28 February 2023
- The Top 5 Cybersecurity threats facing Businesses Today - 28 February 2023